Microsoft is warning out about MalLocker.B, a new mobile ransomware.
This one takes advantage of the Android’s “incoming call” notifications and Home button, which locks the device and follows to show a ransom note.
It’s known for being inserted into malicious websites and online forums through social engineering lures, disguising as popular apps and craked games.
But be aware, because it’s not the first well-known ransomware from the Android family. It just has revived with new techniques and mechanisms to evade security.
MalLocker.B Ransomware Steals Data with Fake Notifications
If you’re a frequent reader of cybersecurity news, this headline won’t result in surprising for you, considering 2020 has been a year full of ransomware attacks (50% increase in the daily average, to be exact).
And it’s estimated that it has worsened in the last three months.
What’s different with MalLocker.B, is that it uses a new method to exploit vulnerabilities.
To compare, previous Android ransomware has attacked the Android accessibility feature “SYSTEM_ALERT_WINDOW.” This permission used to display fake police alerts on top of the screen, to find and steal images inside the device.
The old method got “patched” by cybersecurity experts and anti-malware software can detect this behavior. Now, the new version is capable of overcoming this barrier.
How does it do it? Basically, a fake call notification is used to alert the victim about an incoming call they have to attend. But what it truly does, is show a pop-up window covering a great part of the screen.
And as with most ransomware attacks, this blocks the user from triggering any “scape” action: in this case, are the Home or Recent keypress which prevent from switching somewhere else.
What does Microsft say about it?
“This creates a chain of events that triggers the automatic pop-up of the ransomware screen without doing infinite redraw or posing as a system window.
This new mobile ransomware variant is an important discovery because the malware exhibits behaviors that have not been seen before and could open doors for other malware to follow.
It reinforces the need for comprehensive defense powered by broad visibility into attack surfaces as well as domain experts who track the threat landscape and uncover notable threats that might be hiding amidst massive threat data and signals.”
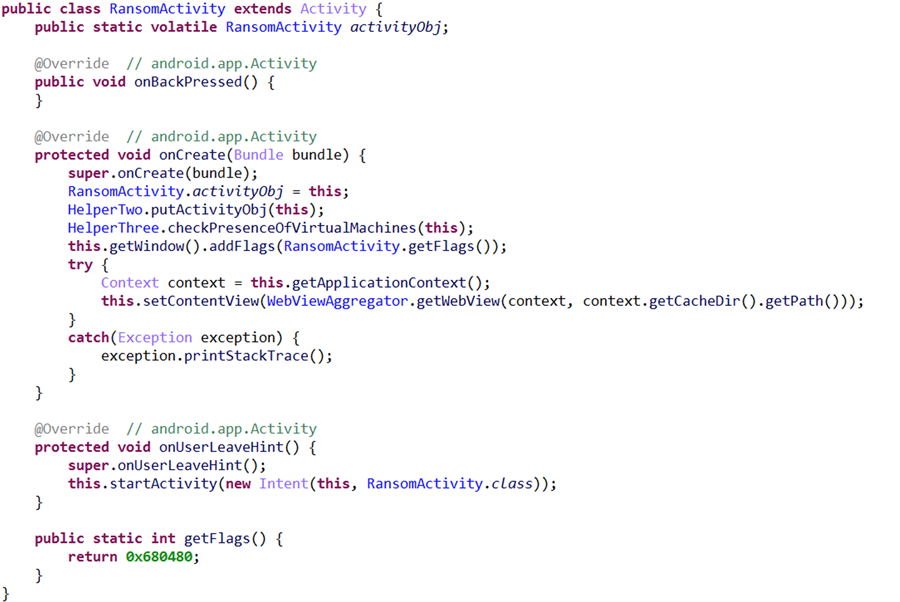
The company also backed up how dangerous its ransomware code is, by describing it as “heavily obfuscated and made unreadable, through name mangling and deliberate use of meaningless variable names and junk code to thwart analysis.”
The malware comes to an obvious conclusion and uses two segments to make the exceptional that triggers the payment screen by means of the callback.
As the scrap-code shows, the malware makes a notice manufacturer and afterward does the accompanying:
A) setCategory(“call”) – This implies that the notice is worked as a significant notice that needs an exceptional advantage.
B) setFullScreenIntent() – This API wires the warning to a GUI so it springs up when the client taps on it. At this stage, a large portion of the task is finished for the malware. Nonetheless, the malware wouldn’t have any desire to rely upon client association to trigger the ransomware screen, along these lines, it adds another usefulness of Android callback.
On Android, an Intent is an item segment that licenses customers to mastermind the components of different Activities to achieve an endeavor. It’s an illuminating item that can be used to request a movement from another application section.
The Intent object conveys a string value boundary (“action”).
The malware makes an Intent inside the unscrambling capacity utilizing the string esteem passed as the name for the Intent. It at that point decodes a hardcoded scrambled worth and sets the “action” boundary of the Intent utilizing the setAction API.
When this Intent item is produced with the activity esteem highlighting the unscrambled content, the decoding capacity restores the Intent item to the callee.
The callee then summons the getAction strategy to get the unscrambled content.